| | Easy Downtime and Workload | 2 mins AWS | Solve |
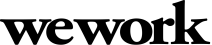
ChickTok is a dating app that runs on EC2 behind an ALB. The EC2 instances run in an EC2 Auto Scaling group across multiple AZ. On every Saturday night, the app becomes atleast 5 times slower. Upon investigation, it is found that the CPU utilization reaches 100% within a matter of seconds instead of being a gradual increment. This is happening due to a batch core dating algorithm update that happens on every Saturday 9PM.
ChickTok wants a solution that
- Tackles the extra workload
- Avoids downtime
Which of the following would you recommend?
|
| | Medium EC2DataProcessing | 2 mins AWS | Solve |
You work as a Solutions Architect for a data analysis firm. The company stores large datasets on Amazon S3, and you've been tasked with setting up an Amazon EC2 instance to process this data. The EC2 instance will fetch data from S3, process it, and then write the results back to a different S3 bucket.
To ensure security, the EC2 instance should not have direct internet access, and it should only be able to communicate with the S3 buckets. You've decided to place the EC2 instance in a VPC private subnet with a CIDR block of 10.0.1.0/24. The associated security group is set to deny all inbound traffic and allow all outbound traffic.
Which additional configuration should you make to enable the EC2 instance to access the S3 buckets while complying with the security requirements?
A: Modify the Network ACL of the subnet to allow outbound connections to the IP range of the S3 service.
B: Assign a Public IP to the EC2 instance and update the security group to allow inbound and outbound traffic to S3.
C: Add a NAT Gateway in the private subnet and update the route tables to direct S3 traffic to the NAT Gateway.
D: Create an S3 VPC Gateway Endpoint and update the route tables for the private subnet to direct S3 traffic to the VPC Endpoint.
E: Create a VPN connection from the VPC to the S3 buckets.
|
| | Medium Orderly Restoration of RDS with Transaction Logs | 3 mins AWS | Solve |
You work as a database manager for a fintech company that uses an AWS RDS PostgreSQL instance. The company abides by stringent data security standards, which require minimal data loss in the event of database failures or accidental data modifications.
Unexpectedly, an operation that updates a significant number of records in a crucial transaction table is mistakenly run. You discover that this operation occurred at 12:45 PM. Your RDS PostgreSQL instance is configured to perform automated backups every day at 1:00 AM, with transaction logs being backed up every 5 minutes. Furthermore, there is a manual DB snapshot taken at 11:00 AM on the same day.
To restore the database with minimal data loss, considering the sequence and order of log application, which of the following steps should you execute?
A: Restore from the manual DB snapshot at 11:00 AM, then perform a point-in-time recovery to 12:45 PM.
B: Perform a point-in-time recovery to 12:45 PM.
C: Restore from the last automated backup at 1:00 AM, then apply all transaction logs until 12:45 PM.
D: Restore from the manual DB snapshot at 11:00 AM, then apply transaction logs from 11:00 AM to 12:45 PM.
E: Perform a point-in-time recovery to 11:00 AM, then apply transaction logs from 11:00 AM to 12:45 PM.
|
| | Medium Push Notifications | 3 mins AWS | Solve |
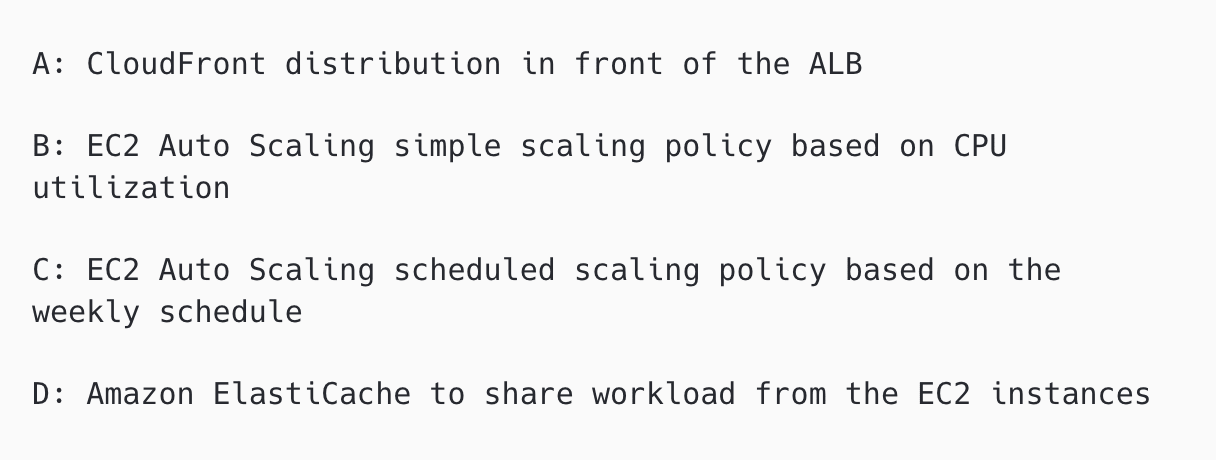
Flowlife is a tips iOS app that is running on AWS with ~10 million users in the US. Users can post tips about a particular place (restaurants, businesses etc) and other users can search for the tips in the app. Flowlife wants to implement location based alerts on their iOS app. Users will receive relevant tips in proximity to their location. For maximum user engagement and relevant tips, the tips must be in the low minute count. Which of the following solutions is cost effective?
|
| | Medium SecureEC2Setup | 2 mins AWS | Solve |
As an AWS Cloud Engineer for a financial institution, you're setting up an EC2 instance in a VPC to host a web application that handles sensitive financial data. The EC2 instance is placed in a private subnet and associated with a security group that only allows inbound HTTPS (port 443) traffic from the internet. You have an Application Load Balancer (ALB) in a public subnet, which forwards incoming traffic to the EC2 instance.
However, during the testing phase, you find that the web application on the EC2 instance is not reachable from the internet, but works fine from within the VPC.
What could be the reason for this?
A: The security group should allow inbound traffic from the ALB's security group, not the internet.
B: The ALB should be in the private subnet, not the public subnet.
C: EC2 instances hosting sensitive data cannot be reached through an ALB.
D: The ALB and EC2 instance must be in the same subnet.
|
| | Medium Backup and Restore Strategy | 2 mins Azure | Solve |
You are a database administrator for an organization that uses Azure SQL Database for its operations. The organization has a strict data retention policy and has set up the following backup strategy:
1. Full backups are taken every Sunday at midnight.
2. Differential backups are taken every day at midnight, excluding Sunday.
3. Transaction log backups are taken every hour on the hour.
On Wednesday at 2:30 PM, a failure occurred, and the latest backup files available are: full backup from the previous Sunday, differential backups for Monday and Tuesday, and transaction log backups up to Wednesday 2 PM.
In order to restore the database to the most recent point in time with the minimum amount of data loss, in what order should you restore the backups?
A: Restore the full backup, then the differential backup for Tuesday, then the differential backup for Wednesday, then each transaction log backup from midnight on Wednesday to 2 PM on Wednesday.
B: Restore the full backup, then the differential backup for Wednesday, then each transaction log backup from midnight on Wednesday to 2 PM on Wednesday.
C: Restore the full backup, then each differential backup from Monday and Tuesday, then each transaction log backup from midnight on Wednesday to 2 PM on Wednesday.
D: Restore the full backup, then the differential backup for Monday, then each transaction log backup from midnight on Monday to 2 PM on Wednesday.
E: Restore the full backup, then the differential backup for Tuesday, then each transaction log backup from midnight on Tuesday to 2 PM on Wednesday.
|
| | Medium Resolving Connection Issues | 2 mins Azure | Solve |
You are an Azure Administrator and you manage a Linux VM running an internal web application in Azure. The web application communicates with a database server hosted on another VM in the same Virtual Network (VNet).
Recently, users have reported that the web application is not accessible. After initial troubleshooting, you have identified that the web application VM is unable to establish a connection with the database server VM on port 5432.
You have checked and confirmed the following:
1. Both VMs are up and running without any issues.
2. Both VMs are located in the same VNet and subnet.
3. Both VMs can successfully ping each other.
4. A Network Security Group (NSG) is associated with the subnet, and it has a rule allowing all outbound traffic from the web application VM.
5. The NSG rule for inbound traffic to the database VM on port 5432 has a higher priority than the default deny all rule.
Given the information provided, what could be the most likely reason for the issue and the appropriate resolution?
A: Add a route table to the subnet to enable communication between the VMs.
B: The NSG rule priority for the inbound traffic to the database VM is not set correctly. Adjust the priority to be lower than the default rule.
C: Check if a firewall is enabled on the database VM that might be blocking the port. If so, configure it to allow connections on port 5432.
D: The issue is related to the DNS resolution. Update the DNS settings in the VNet to enable name resolution between the VMs.
E: The web application is not correctly configured to connect to the database. Update the connection string in the web application configuration.
|
| | Medium Resolving NSG Configuration Issues | 2 mins Azure | Solve |
You are an Azure Administrator in a software development company. A Linux VM is deployed on Azure, hosting an application server running on port 5000, set to start whenever the VM is booted up.
The VM is associated with a Network Security Group (NSG) having the following inbound security rules:
- Rule 100 (Priority: 100): Allow SSH (port 22) from any source
- Rule 200 (Priority: 200): Allow HTTP (port 80) from any source
- Rule 400 (Priority: 400): Allow TCP traffic on port 5000 from any source
- Rule 300 (Priority: 300): Deny all inbound traffic from any source
The outbound security rules are configured to allow all traffic to any destination.
Internal users have been attempting to connect to the application server on port 5000 but they are consistently facing connection timeouts. You've confirmed the application server is up and running, and you can connect to the server locally on the VM.
What is the most probable cause of the problem and how would you fix it?
A: The inbound rule to allow TCP traffic on port 5000 is conflicting with the rule to allow HTTP on port 80. Remove Rule 200.
B: Rule 300 to deny all inbound traffic is being processed before Rule 400 to allow traffic on port 5000. Modify the priority of Rule 400 to a value less than 300.
C: The application server should be configured to listen on a well-known port instead of port 5000. Change the server settings.
D: The NSG is missing an inbound rule to allow ICMP traffic. Add a new rule with a lower priority.
E: The NSG needs to have an outbound rule specifically allowing traffic to port 5000. Add a new outbound rule.
|
| | Medium Healthy Replica | 2 mins Google Cloud Platform | Solve |
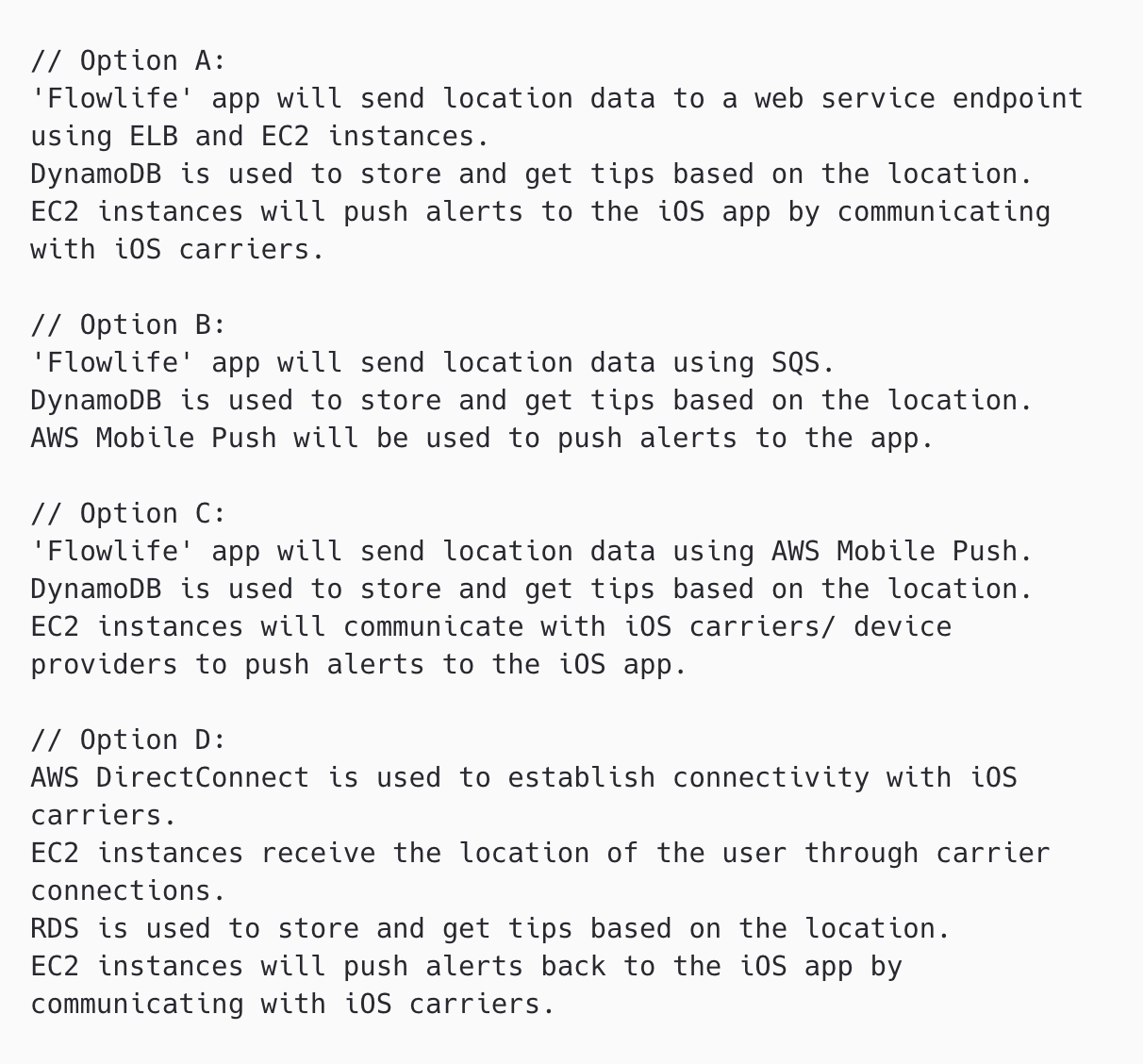
Sam Sankman works as Cloud Associate at FTXX Inc. FTXX’s core application is deployed in a Google Kubernetes Engine cluster. When a new version of the application is released, CI/CD tool updates the spec.template.spec.containers[0].image value to reference the Docker image of the new application version. When the Deployment object applies the change, Sam wants to deploy at least 1 replica of the new version and maintain the previous replicas until the new replica is healthy. Which change should Sam make to the Kubernetes Engine Deployment object shown below?
A: Set the Deployment Strategy to Rolling Update
B: Set the Deployment Strategy to Recreate
C: Set maxSurge to 0
D: Set maxSurge to 1
E: Set maxUnavailable to 0
F: Set maxUnavailable to 1
|
| | Medium Network Rules | 3 mins Google Cloud Platform | Solve |
Depp works as Google Cloud Architect at Amber Inc. Deep created an instance with following firewall rules:
NAME: ssh-allow
NETWORK: testnet
DIRECTION: INGRESS
PRIORITY: 100
ALLOW: tcp:22
NAME: deny-everything
NETWORK: testnet
DIRECTION: INGRESS
PRIORITY: 400
DENY: tcp:0-65535,udp:0-6553
What would happen if Depp tries SSH to the instance now?
A: SSH would be denied as the deny rule overrides the allow
B: SSH would be allowed as the allow rule overrides the deny
C: SSH would be denied and would need instance reboot for the to allow rule to take effect
D: SSH would be denied and would need gcloud firewall refresh command for the allow rule to take effect
|
| | Easy Storage Costs | 2 mins Google Cloud Platform | Solve |
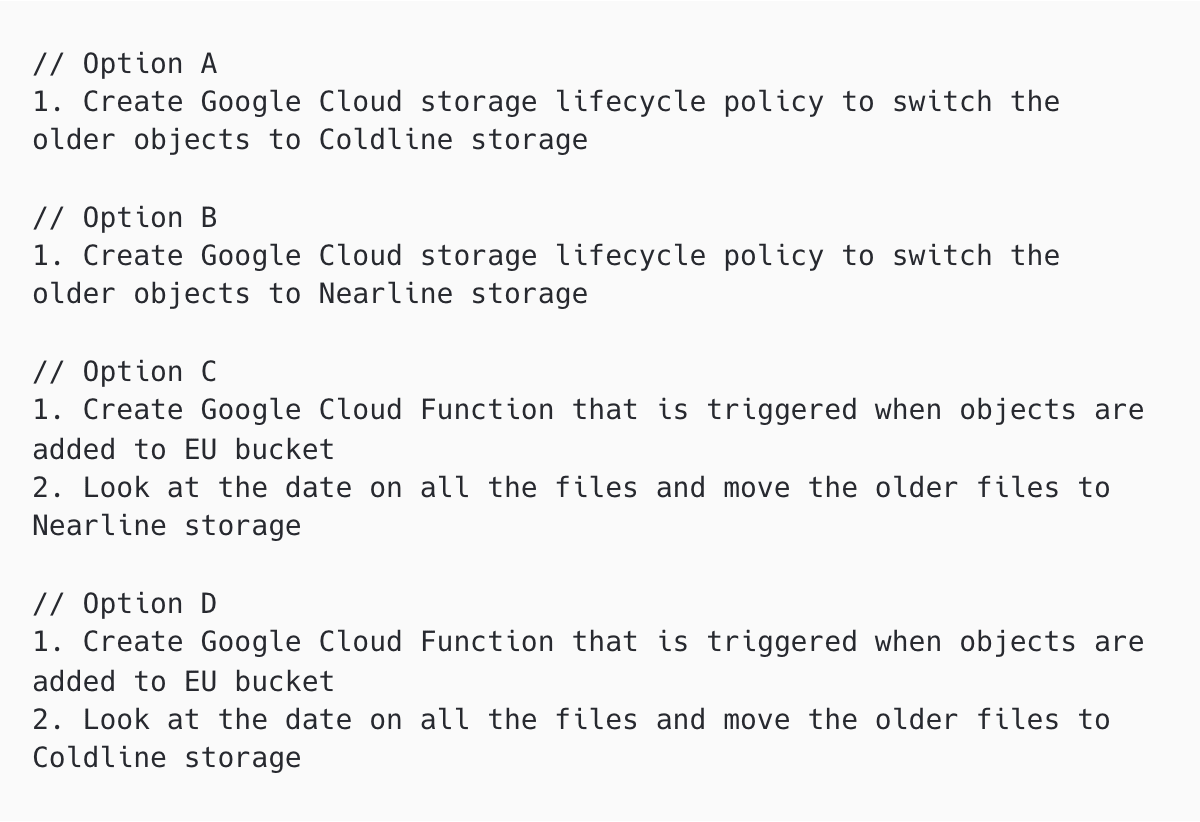
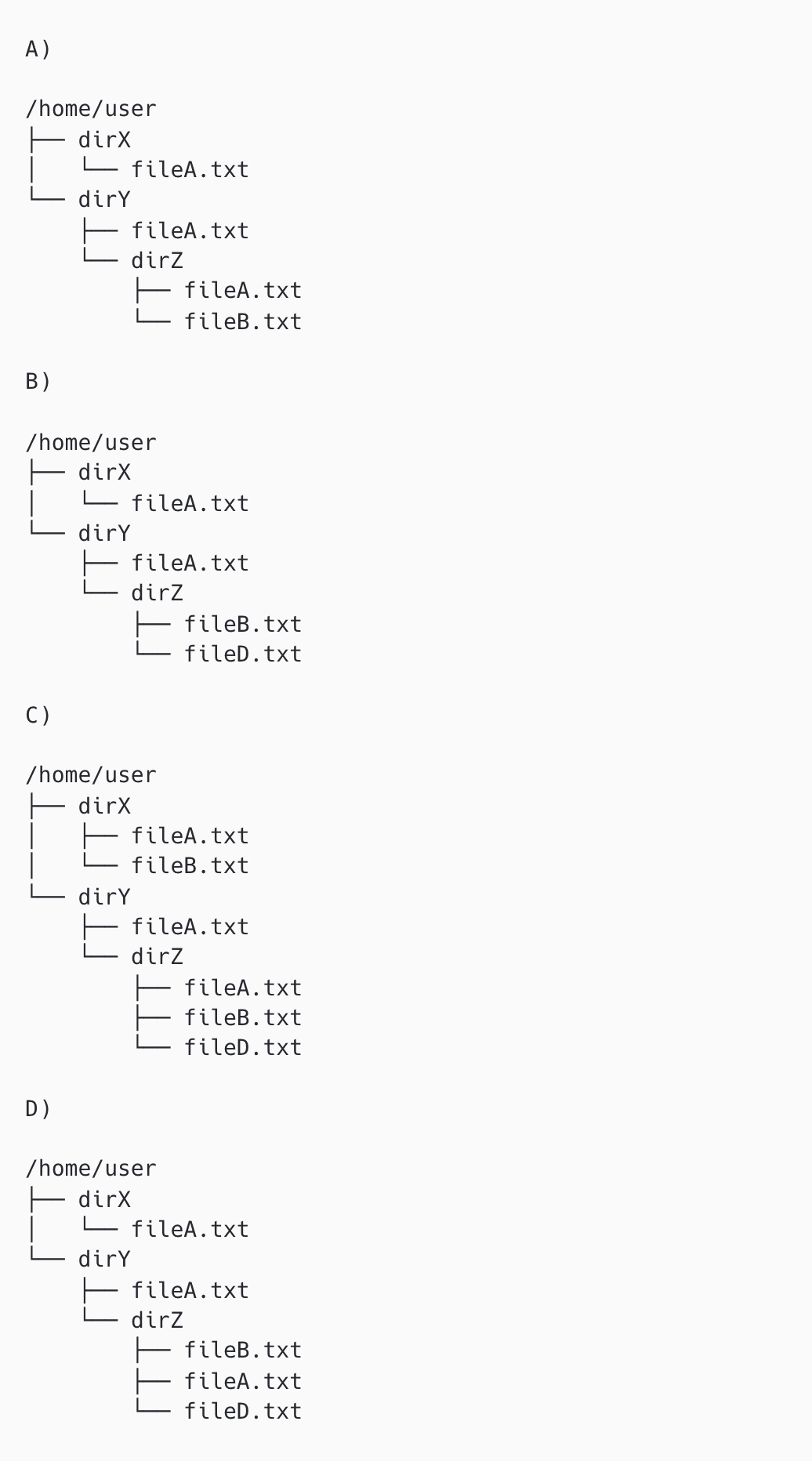
Kloo is a social media platform similar to Twitter in the EU market and uses Google Cloud for their infrastructure requirements. Kloo generates multiple files per day. Owing to data regulations, Kloo has to store these files in the EU regional bucket. Kloo’s data team needs only the files of last 14 days for their algorithms and APIs but need to store every single file for safe keeping and regulatory purposes even though the past data is rarely accessed. Given these constraints, how can Kloo’s data team lower the storage costs?
|
| | Medium Storage in Compute Recovery | 3 mins Google Cloud Platform | Solve |
You work as a data manager for a large e-commerce company that heavily relies on a PostgreSQL database running on a GCP Compute Engine instance. The company has a well-established backup policy, which includes:
1. Full database backup every Monday at 1:00 AM.
2. Differential backup every day at 1:00 AM, except Monday.
3. Transaction log backup every 30 minutes.
These backups are stored in Google Cloud Storage. Today is Thursday, and a data corruption incident occurred at 4:15 PM. You have the following backup files available:
1. Full backup: Full_Backup_Mon.bak taken on Monday 1:00 AM.
2. Differential backups: Diff_Backup_Tue.bak, Diff_Backup_Wed.bak, Diff_Backup_Thu.bak taken at 1:00 AM on their respective days.
3. Transaction log backups: 30-minute interval backups from Monday 1:30 AM until Thursday 4:00 PM, like TLog_Backup_Thu_1530.bak, TLog_Backup_Thu_1600.bak.
Given the RPO (Recovery Point Objective) of 30 minutes, which of the following sequences of restore operations would ensure minimal data loss?
A: Full_Backup_Mon.bak, Diff_Backup_Thu.bak, then Transaction Log backups from Thursday 1:30 AM to 4:00 PM.
B: Full_Backup_Mon.bak, Diff_Backup_Wed.bak, then all Transaction Log backups from Wednesday and Thursday.
C: Full_Backup_Mon.bak, Diff_Backup_Thu.bak, then all Transaction Log backups from Thursday.
D: Full_Backup_Mon.bak, then all Transaction Log backups from Monday to Thursday 4:00 PM.
E: Full_Backup_Mon.bak, Diff_Backup_Tue.bak, Diff_Backup_Wed.bak, Diff_Backup_Thu.bak, then Transaction Log backups from Thursday 1:30 AM to 4:00 PM.
|
| | Medium Debugging Issues | 2 mins Linux | Solve |
You are working on a Linux system and have recently installed a new program named myprogram. The executable is located in /opt/myprogram/bin/. You want to be able to run this program from any directory in your shell without specifying the full path.
You executed the following command:
export PATH="/opt/myprogram/bin"
However, when you try to run the program using myprogram, you get the following error message:
-bash: myprogram: command not found
Which of the following commands can fix this issue and allow you to run the program?
A: export PATH=$PATH:/opt/myprogram/bin/
B: export PATH="/opt/myprogram:$PATH"
C: export PATH="/opt/myprogram/bin:$PATH"
D: ln -s /opt/myprogram/bin/myprogram /usr/local/bin/myprogram
|
| | Easy File Structure and Navigation | 2 mins Linux | Solve |
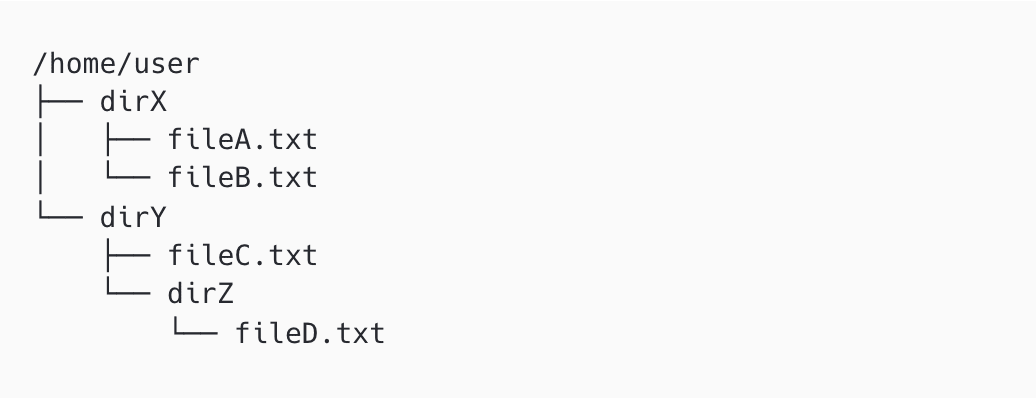
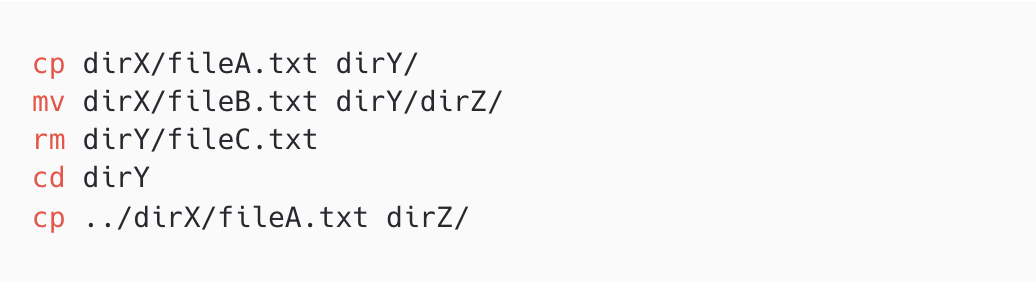
Consider the following directory structure:
You start at /home/user and execute the following commands:
What will be the resulting directory structure?
|
| | Medium Fork mellow yellow | 2 mins Linux | Solve |
How many times will the following code will print "Mellow Yellow"?
|
| | Medium Remote server connection | 2 mins Linux | Solve |
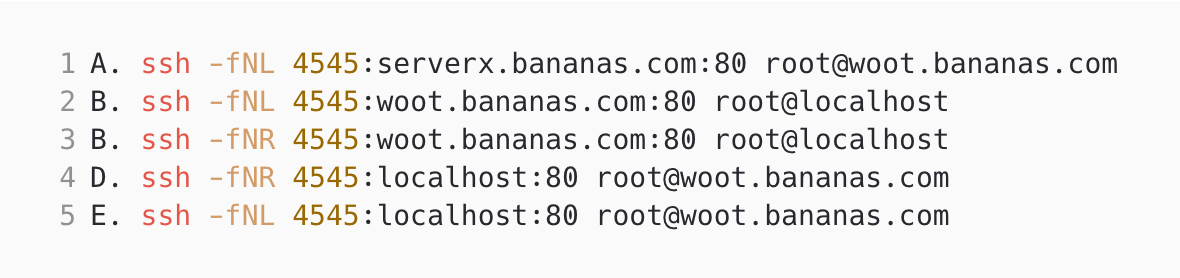
Our software engineering intern, Wu is looking to use port 4545 on localhost to connect to a remote server called woot.bananas.com on port 80. Which command would you recommend for this?
|